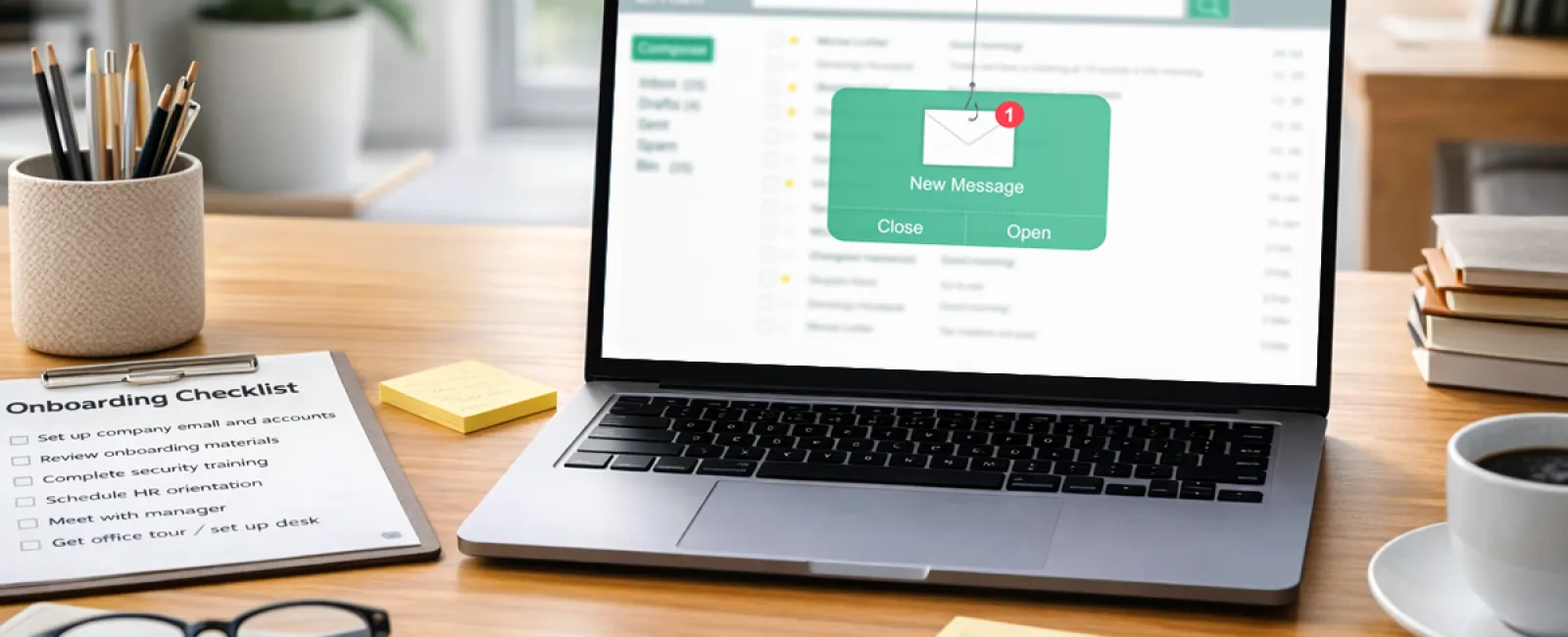
An email lands on a Tuesday morning.
It appears to come from the CEO. The name checks out. The wording feels believable. Even the signature seems authentic.
"Hey — can you help me with something quickly? I'm stuck in back-to-back meetings. I need you to handle a vendor payment. I'll explain later."
The new hire hesitates.
They've only been with the company for four days. They're still learning the workflow, still unsure what counts as normal, and definitely not eager to challenge the CEO during their first week.
So they comply.
And in one click, the damage is already underway.
Why week one is the highest-risk moment
Each spring, organizations welcome a fresh group of employees, many of them recent graduates and summer interns stepping into their first professional roles. For companies, that means onboarding season. For cybercriminals, it means opportunity.
Keepnet Lab's 2025 New Hires Phishing Susceptibility Report found that CEO impersonation emails are 45% more likely to succeed against new hires than experienced staff.
Attackers don't usually target the most seasoned people on your team. They focus on employees who are still learning because the early days create a gap where everything feels unfamiliar and nothing feels fully certain.
A new employee may not know what a legitimate request looks like. They don't yet understand how the CEO normally communicates. They haven't built the instincts or confidence that come with time, and attackers exploit that uncertainty.
But here's the real issue: the new employee isn't the weakness. The greatest risk isn't the person trying to be helpful. It's the system that hasn't guided them yet.
If you manage a business, you probably already know which team member would be most likely to respond quickly.
The real problem isn't training alone. It's the setup.
Think back to that employee's first day.
The laptop wasn't ready. Access wasn't fully provisioned. Their email account was still being created. They borrowed a coworker's login to check something fast. They saved a file locally because the shared drive wasn't available. They used their personal phone to look up a client number because it was quicker.
None of that felt dangerous. It felt practical. Resourceful. Like the smart thing to do on a hectic first day.
Yet during that first week, while everything is still being assembled, several risks quietly appear. Shared credentials create untracked access, files move outside backup systems, personal devices touch company data, and no one explains what to do when something looks suspicious.
Keepnet's report also shows that new employees are 44% more likely to fall for phishing than tenured staff. That difference isn't caused by recklessness. It's caused by disorder. When onboarding is messy, security becomes an afterthought. That's exactly the kind of environment a phishing email is designed to exploit.
The attack didn't create the weakness. The first day did.
What a secure first day should include
Solving this doesn't require an hour-long security lecture. It requires three essentials to be in place before the new hire arrives.
1. Their access is prepared, not patched together.
That means the laptop is ready, credentials are issued, and permissions are clearly defined. No shared logins, no temporary fixes, and no "we'll handle that later this week."
2. They understand what normal communication looks like in your business.
This can be a quick 10-minute conversation. Does the CEO ever request payments by email? Does anyone? What should they do if something feels suspicious? This isn't full-scale training; it's essential orientation.
3. They have a safe place to ask questions without embarrassment.
The employee who paused before clicking that message probably would have asked someone if they knew who to turn to. Most first-week mistakes happen quietly because new hires don't want to appear inexperienced.
Give them a person. Give them a process.
Most security failures don't happen because someone intentionally breaks the rules. They happen because the rules haven't been made clear yet.
Maybe your onboarding is already strong. Maybe your team is small enough that first days feel more personal than procedural. But if you've ever watched a new hire improvise through week one — or if you're planning to bring someone on this spring — it's worth addressing before that Tuesday email shows up.
Click here or give us a call at 817-277-1001 to schedule your free 15-Minute Discovery Call.
And if you know another business owner who's hiring soon, pass this along. The smartest time to lock the door is before anyone tries it.